The deep web of the internet shrouds a realm of anonymity, accessible only through unique connections known as onion links. These paths point to hidden services, which operate on the Tor network. Accessing these platforms requires specialized software like Tor and a willingness to venture into the uncharted.
Tucked inside this digital hidden world, you'll discover a varied mix of content, ranging from lawful forums for whistleblowers to questionable marketplaces. Journeying this landscape requires awareness, as the line between truth can often be blurred.
Deep Dive into the Darknet's Labyrinth
The darknet, a anonymous realm shrouded in mystery and controversy, awaits those brave enough to descend. A labyrinth of private networks, it presents both opportunities and obscure knowledge. Navigating its depths onionlinks requires caution, as the lines between reality often become blurred.
- Anonymists lurk in the shadows, exploiting on vulnerabilities.
- Black markets are traded with discretion.
- Governments probe this hidden world, striving to maintain order.
The darknet's intricacies continue to challenge researchers and society alike. Its impact on our world is undeniable, raising legal questions that demand debate.
Exploring Onion Routes: A Beginner's Guide
So you're intrigued about the sphere of onion routes? These multifaceted networks present a unique path for obscurity online. But navigating them can appear like decoding a puzzle. Fear not, rookie, this overview will cast some light on the basics of utilizing onion routes.
- Initially,{ you'll need to obtain a specialized software known as Tor. This suite will mask your interactions, making it difficult for others to monitor your online movements.
- After that,{ you can access onion sites, which {feature|.onion domain extensions. These sites are often used for a variety of functions, from sharing sensitive information to conducting anonymous interactions.
- Be aware that the onion route is not unbreakable. It's important to employ good cybersecurity habits, such as using strong passphrases and being vigilant about the information you share.
At its core, onion routes can be a valuable tool for preserving your anonymity online. Nonetheless, it's crucial to comprehend the potential dangers involved and use them judiciously.
The Art of Concealment: Onion Link Encryption
In the realm within digital communication, safeguarding sensitive information is paramount. Enter layered link encryption, a potent method for secure data transmission. This intricate process shields messages via multiple layers with encryption, akin to the concentric layers of an onion. Each layer consists of unique cryptographic key, hindering access with regard to the message's content without all corresponding codes.
- This layered approach conceals the information, building a robust shield against illegitimate access. Moreover, if one layer becomes compromised, the remaining layers remain to secure the data's integrity.
- As a result, onion link encryption offers a high level in security, making it an invaluable asset for safeguarding sensitive information in the digital sphere.
Exposing Secrets in a Digital Fortress
The .onion domain—a shrouded realm where anonymity reigns supreme. It stands as a bastion for private communication, a digital fortress shielding users from prying eyes. Yet, beneath this veil of obscurity lies a complex web of interactions, some benign, others suspect. Unmasking these hidden networks requires advanced tools and a keen understanding of the digital landscape. Authorities and researchers alike are exploring new methods to pierce this veil, revealing the inner workings of .onion communication.
The rise of digital assets on the dark web has further intensified the challenges. These decentralized systems offer an ideal platform for underground transactions, making it difficult to trace the flow of funds and identify those involved. The .onion ecosystem is a constantly adapting landscape, presenting a daunting obstacle to law enforcement and cybersecurity experts.
Unveiling the Realities of Onion Links
Onion links are more than just a way to reach hidden content. They represent a intriguing world built on layers of security. These links, often used by whistleblowers and activists, ensure a measure of secrecy from curious eyes. Exploring onion links is like embarking on a journey into the underworld.
- While they can be used for legal purposes, onion links are often associated with illegal activities. It's important to demonstrate caution when navigating this hidden territory.
- Understanding the structure of onion links can shed light on their impact on society.
If you're a tech enthusiast or simply interested, the world of onion links offers a intriguing glimpse into the evolution of the internet.
 Luke Perry Then & Now!
Luke Perry Then & Now! Julia Stiles Then & Now!
Julia Stiles Then & Now! Elin Nordegren Then & Now!
Elin Nordegren Then & Now! Barbara Eden Then & Now!
Barbara Eden Then & Now!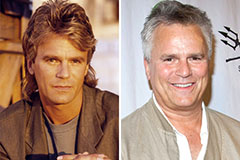 Richard Dean Anderson Then & Now!
Richard Dean Anderson Then & Now!